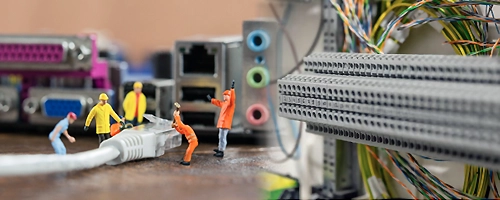
TimeTec offers complete Network Infrastructure solutions alongside our comprehensive PropTech ecosystem, delivering seamless connectivity to support smart building operations. From structured cabling to high-performance network equipment, our infrastructure services are designed to integrate flawlessly with TimeTec’s PropTech solutions—including smart access and elevator control, ELV & IoT automation, smart cashless and touchless parking, visitor management and etc., ensuring a reliable, scalable, and future-ready environment for modern commercial and residential buildings.
What Is a Well-Designed Network Infrastructure?
A well-designed network infrastructure is essential for any organization that relies on technology to operate effectively. It provides the foundation for integrating emerging technologies and new applications, allowing businesses to remain agile, up-to-date, and competitive in their industries.
For service providers, building a robust network infrastructure means ensuring scalability, high availability, and intelligent load balancing. These elements are critical to maintaining seamless connectivity and reliable system performance—key factors in today’s fast-paced digital environment.
Since network interruptions can never be entirely avoided, it's also vital to adopt streamlined network architectures and automated management tools. These help network administrators quickly identify, isolate, and resolve issues, minimizing downtime and ensuring optimal network functionality.
Phone Lookup - Reverse
The Digital Guardian: The Evolution and Impact of Reverse Phone Lookup
However, the proliferation of such powerful tools also raises significant questions regarding privacy and data protection. While many services rely on legally accessible public data, the ease with which personal details can be retrieved has prompted some individuals to take measures to make their numbers unsearchable . Common strategies include removing phone numbers from social media, blocking Caller ID, or requesting removal from data broker sites. This ongoing tension between the need for transparency—to identify unknown callers—and the right to privacy highlights the complex role that reverse phone lookup plays in the digital age. REVERSE PHONE LOOKUP
The primary utility of reverse phone lookup lies in its ability to serve as a first line of defense against the rising tide of digital intrusion. In the contemporary landscape, individuals are frequently bombarded by automated "sniffers"—telemarketers and scammers who use high-volume VOIP systems to dial thousands of numbers simultaneously. These systems often assign fake numbers to caller IDs, making it difficult for recipients to discern legitimate calls from fraudulent ones. By using a reverse lookup service , users can quickly verify if a caller is a potential scammer or a legitimate business partner, effectively putting the power of interaction back into the hands of the recipient. The Digital Guardian: The Evolution and Impact of
In an era where communication is instantaneous and digital footprints are pervasive, the "reverse phone lookup" has transitioned from a niche investigative tool to a fundamental utility for the average consumer. At its core, a reverse phone lookup is a specialized search mechanism that allows individuals to identify the owner of an unknown phone number by entering it into a database. While traditionally used to uncover basic details like a name or address, modern iterations of this technology have become sophisticated instruments for personal security and information management. This ongoing tension between the need for transparency—to
Beyond simple identification, these tools offer a range of practical applications for various demographics. For small business owners, it serves as a screening tool for prospective clients or suppliers. For families, it allows parents to monitor unknown contacts their children may receive and helps caregivers protect elderly relatives from financial fraud. The information provided can be surprisingly comprehensive; services like CocoFinder can return data including current and past addresses, associated service providers, and even links to social media accounts. This depth of information is often compiled from a vast array of sources, including public records, business lists, and social media, though the accuracy of these services can vary based on the quality of their underlying databases.
In conclusion, reverse phone lookup has evolved from a simple directory service into a multi-faceted tool for security, business, and personal connectivity. While it is not a perfect solution—given that scammers can spoof numbers and databases may contain outdated information—it remains an essential resource for navigating a world of constant communication. As digital interactions continue to grow, the balance between utilizing these identifying tools and protecting personal privacy will likely remain a central theme in our connected society. How Reverse Phone Lookups Work [with OSINT Industries]